The Evolution of Application Security:
From Manual to AI-Powered and Beyond
by Ali Naqvi
Application security has come a long way, from manual processes to advanced AI-powered solutions that are faster and more adaptive. With today’s advanced cyber threats, Artificial Intelligence (AI), Machine Learning (ML), and Deep Learning (DL) are changing application security and will bring even smarter defenses in the future. In this post, I will cover the past and present approaches, current AI techniques, and what’s to come in application security.
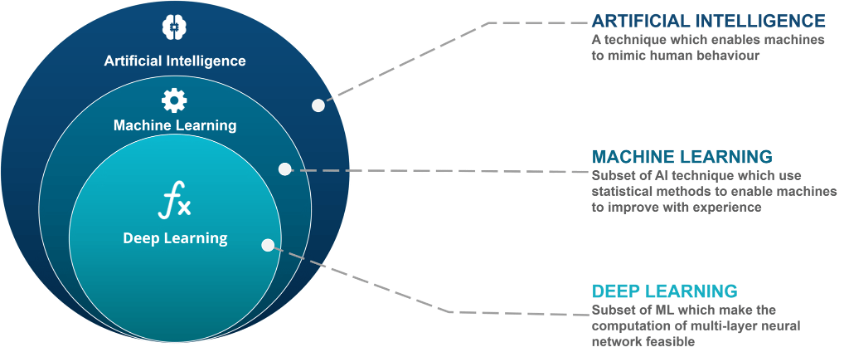
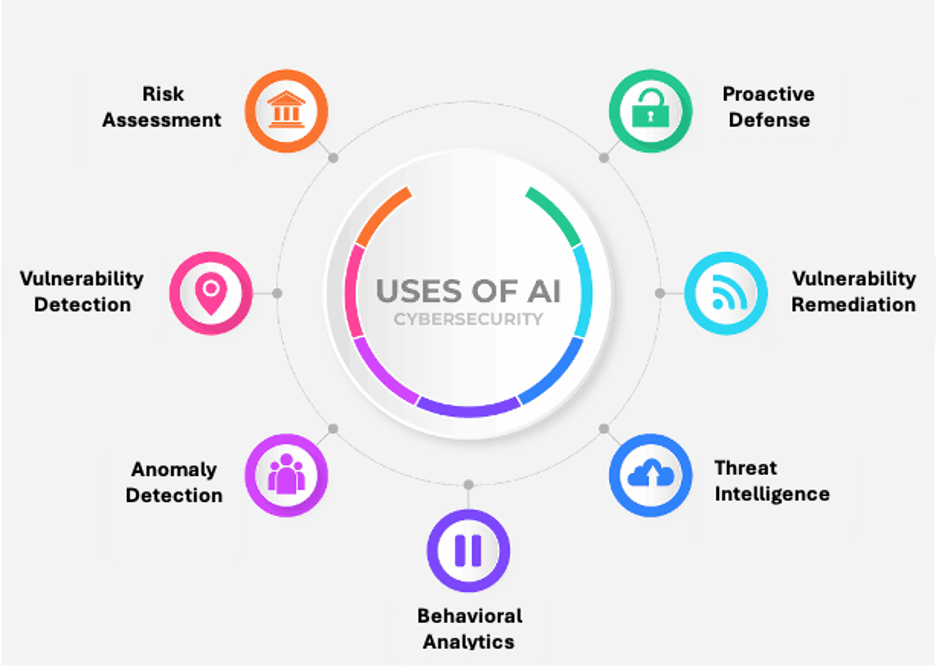
Application Security Artificial Intelligence (AI), in a nutshell, allows machines to do tasks that would typically require human intelligence, like decision-making and pattern recognition. Machine Learning (ML), a subset of AI, enables applications to learn from data provided to the application and get better over time without having the developers program each scenario they want the application to handle. Deep Learning (DL), a further subset of ML, uses complex neural networks to recognize intricate patterns in large datasets, making it especially powerful in detecting sophisticated security threats and identifying complex vulnerabilities. As these technologies advance, new applications utilize AI, ML, and DL to secure organization’s applications. Some of these include automation detection and response for vulnerabilities found, prioritizing the remediation of vulnerabilities, and helping with the remediation of new threats. I will touch on some of the most popular AI techniques used in application security today and what’s to come.
Key AI Techniques in Use Today
1.
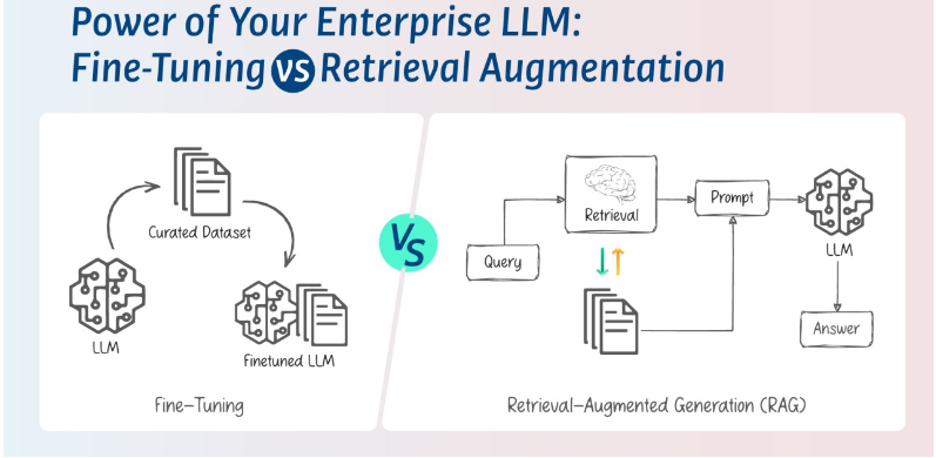
Fine-Tuning: Fine-tuning customizes pre-trained AI models for specific tasks, such as identifying unique vulnerabilities in an environment. This allows you to create task-specific AI apps without building models from scratch. (Fine Tuning)
2.
Retrieval-Augmented Generation (RAG): RAG pairs language models with a retrieval system so they can pull in the latest context-specific data to make real-time decisions. RAG is great for gathering threat intel, explaining written code to developers, and allowing security analysts to ask security-related questions with a chatbot. (RAG)
3.
AI Agents: AI agents run autonomously to do specific security tasks, like monitoring networks and responding to threats. They do the routine stuff so your human teams can focus on the hard stuff. Companies like Microsoft and ServiceNow incorporate AI agents in their product line. (Servicenow AI Agents) (Microsoft AI Agents)
4.
Behavioral Analytics: Behavioral models detect anomalies by understanding typical user behavior, which makes it easier to spot insider threats or compromised accounts. (Behavioral Analytics)
5.
Explainable AI (XAI): XAI makes AI decisions transparent so you can see why certain anomalies or vulnerabilities were flagged. This is important in regulated industries like finance and healthcare, where organizations must provide proof and a trail of changes being made. NIST, SOC2, and HIPPA are examples of these regulations. (Explainable AI)
In upcoming blogs, I will discuss these techniques, the tools you can use to incorporate them, and how they work in more detail.
A Comparison of Application Security: Past, Present, and Future
As AI changes continue to change everything, here’s how application security has evolved:
1.
Vulnerability Detection and Management
In the past, vulnerability detection was done through manual scans and code reviews, which took time and often missed real-time risks. Today, tools like Snyk and SonarQube continuously scan and prioritize risk so security teams can address vulnerabilities based on real-time risk assessments. With new techniques like AI agents, we will start seeing new security tools that detect and fix vulnerabilities, creating a continuous security feedback loop with minimal human intervention.
2. Anomaly Detection and Behavioral Analytics
In the past, Anomaly detection was based on static rules, identifying threats based on known patterns but missing subtle or novel attack methods. Today, threat detection tools like Darktrace create normal activity baselines and detect deviations that indicate potential threats to reduce false positives. We can anticipate seeing tools that will utilize Behavioral analytic models to be predictive so security systems can anticipate risks.
3. Threat Intelligence and Proactive Defense
Threat intelligence was manual and reactive in the past, and organizations couldn’t stay ahead of emerging threats. Today, Recorded Future (acquired by Mastercard) collects and analyzes threat intelligence in real-time so security teams can respond to them. With proactive defense, multi-source integration will update threat profiles from multiple sources in real-time. The future for proactive defense will be AI-driven predictive threat modeling using RAG and NLP, allowing security tools to identify potential attack methods before deployment so security can adjust ahead of time.
Conclusion:
Application security has moved from reactive, manual to AI-driven, real-time defenses that adapt to changing threats. Technologies like fine-tuning, RAG, and autonomous AI agents will continue to elevate application security to new heights. The future of AI in security will be self-learning, adaptive systems that can predict threats before they occur. As this happens, organizations will be better equipped to deal with complex threats and create a more secure, resilient, and responsive digital landscape.