Cracking the Code:
Why Application Vulnerability Remediation Is Falling Short
by Ali Naqvi
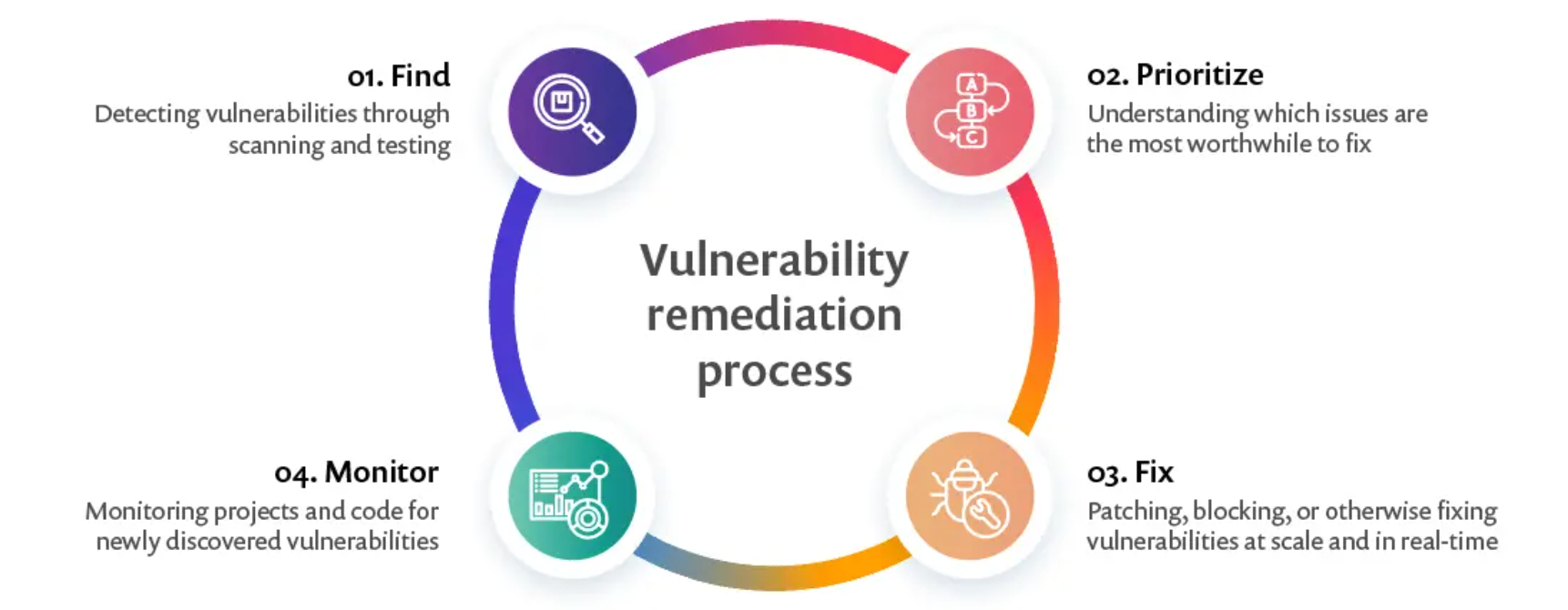
Organizations typically follow a four-step vulnerability remediation process outlined in the article from Snyk. The method includes finding the vulnerability, prioritizing it, fixing it, and monitoring it.
In this blog, I will focus on the “fix” part of the remediation process. Application vulnerability remediation has been a hot topic since organizations started seeing malicious threat actors targeting their applications. Today, organizations are still struggling to remediate the long list of vulnerabilities discovered by security tools. This is primarily due to the complexity of application development. Developers write proprietary code and utilize open-source packages, introducing vulnerabilities into their applications that a threat actor can use for malicious acts. Applications are scanned with scanners to identify and remediate vulnerabilities, which is not an easy task. Security teams have the tools to identify the vulnerabilities but lack access to the code to fix them. Organizations have started adding processes and tools to compensate for the security teams’ not having access to the code required to fix the vulnerabilities. Although this helps, more needs to be done to remediate vulnerabilities quickly and efficiently by assisting the developers tasked with remediating these vulnerabilities.
One feature of these security tools is orchestrating tickets for developers to help with remediation. They integrate with systems like Jira or ServiceNow and open tickets for every vulnerability they find in their scans, which can become inefficient for an organization. A developer may receive multiple tickets pointing to the same problem in the codebase that needs to be fixed. This creates a bottleneck for the developers. They struggle to remediate all the vulnerabilities these security tools found without assistance and continue producing code for the company. Vulnerabilities mount up and expose businesses to hazards they might not be aware of. This backlog of problems will only worsen without improved tools and processes. Organizations are trying to incorporate the following tactics to alleviate this problem, which is a step in the right direction.
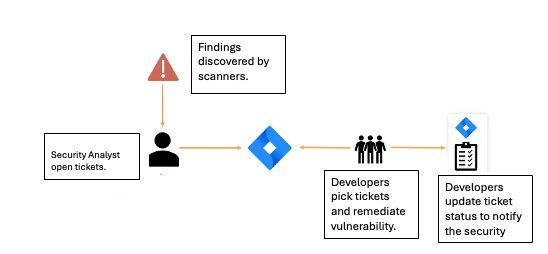
1. Root Cause Analysis for Ticketing Orchestration
Some newer scanning tools have evolved to concentrate on root cause analysis, allowing them to prioritize and open fewer tickets to orchestrate to the developers for remediation. This enables developers to address multiple vulnerabilities simultaneously. Although this helps organizations lessen the number of vulnerability tickets opened for developers to remediate, developers are still drowning in SAST and SCA vulnerability tickets produced by these security tools. This issue mainly exists because developers still bear all responsibility for vulnerability remediation. They still need to take time out of their development time to research and fix these vulnerabilities.
2. "Shifting Left" with developer-friendly processes
The idea of "Shifting Left," moving security earlier into the development process, is a decent beginning to helping developers remediate quickly and efficiently. This allows developers to detect vulnerabilities before they reach production. Shifting left alone will only increase the burden on developers with heavy workloads. Supplementing the shift left with developer-friendly processes can help developers remediate vulnerabilities quickly. Examples of these processes include building remediation time into sprints, setting escalation processes for vetted critical vulnerability remediation, and incorporating vulnerability remediation SLAs. These processes and the "Shift Left" approach can enhance developer productivity for remediation while leaving room for improvement in addressing vulnerabilities.
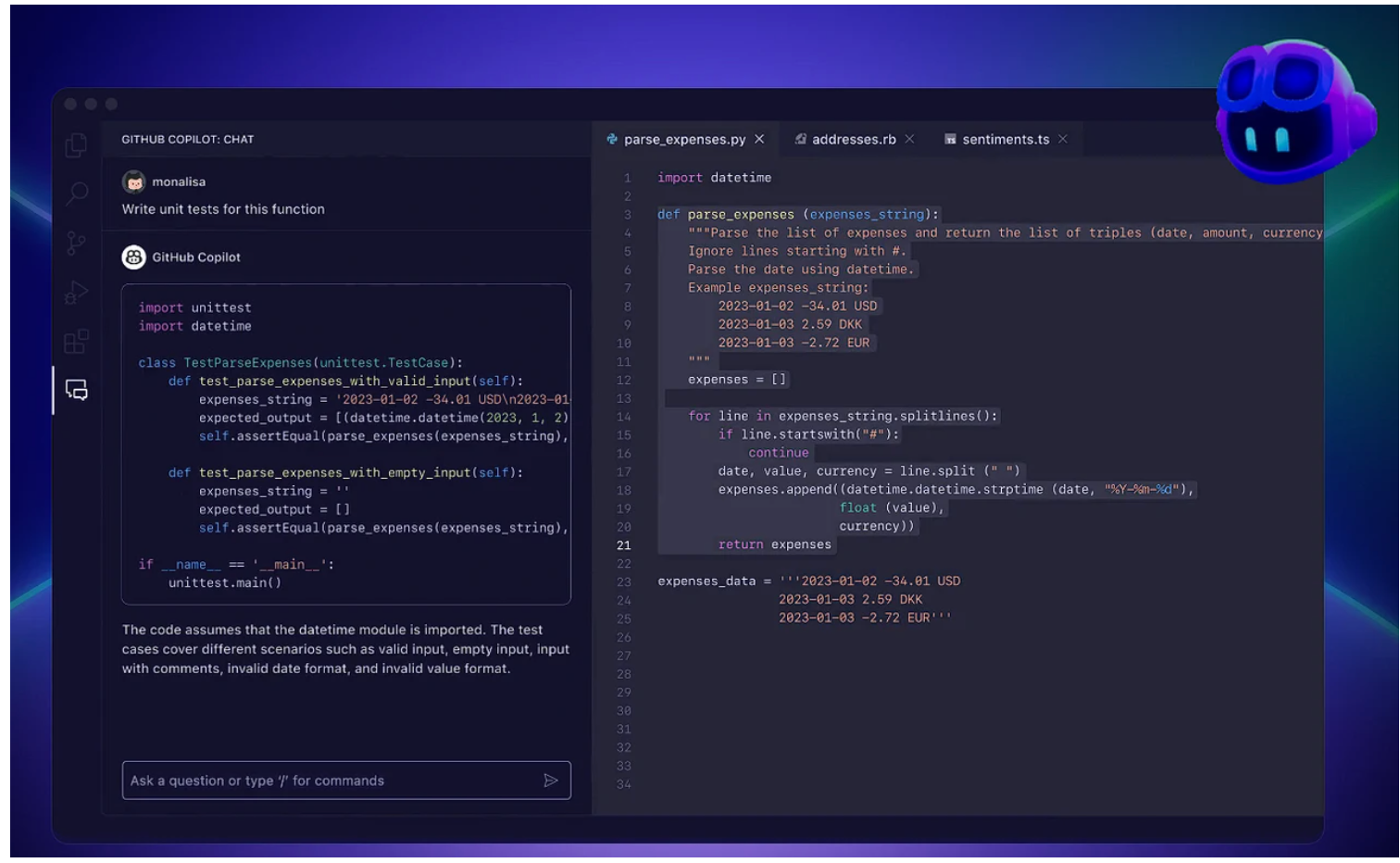
3. AI Assisted Coding
These days, AI seems to have become an answer to most problems. Using AI to help with remediation isn’t any different. One approach organizations use is to incorporate security into developer tools to leverage AI in finding, understanding, and making security recommendations as developers write their code. The tools are integrated into the developer's IDE and offer real-time code fixes for vulnerabilities as the developer writes his code. This helps circumvent insecure code during the development process but overlooks remediation of vulnerabilities after the application has reached production, solving only part of the issues that need to be addressed. The approach needs to be supplemented with post-production scans that the security teams run to prioritize the vulnerabilities for the developers for remediation.
Conclusion
We still have a long road ahead, notwithstanding these advances in security and developer tools. The present paradigm, in which developers only answer for fixing vulnerabilities, is profoundly defective. Already under pressure to provide features under strict constraints, developers are burdened with additional duties for remediating unsustainable security flaws. Organizations must work with developers and provide the right tools to properly remediate vulnerabilities without interfering with their daily operations. Smarter, AI-driven technologies that can fit into the developer environment and integrate deeper into the security and development processes are essential to help developers remediate these application vulnerabilities. This is not a futuristic idea; this is what we at LockDown Labs are working on in the hopes of completely changing how we address application vulnerability remediation—more on this in future blogs.